Personal Surveillance Technologies
News
- EPIC Complaint Leads to Halt of Stalker Spyware Distribution. Following an EPIC complaint, a federal court has orderedCyberSpy Software to stop selling malicious computer software. In March, EPIC filed a complaint with the Federal Trade Commissionalleging that the spyware purveyor engages in unfair and deceptive practices by: (1) promoting illegal surveillance; (2) encouraging "Trojan Horse" email attacks; and (3) failing to warn customers of the legal dangers arising from misuse of the software. The federal regulators agreed, and asked the courtfor a permanent injunction barring sales of CyberSpy's "stalker spyware," over the counter surveillance technology sold for individuals to spy on other individuals. The court entered a temporary restraining order on November 6, 2008. Further litigation is expected before the court rules on the government's request for a permanent ban. For more information, see EPIC's Domestic Violence and Privacypage. (Nov. 17, 2008)
- EPIC Urges Senate to Crack Down on Spyware.EPIC Executive Director Marc Rotenberg presented testimonyon Spyware in a hearingbefore the Senate Commerce Committee. EPIC said Internet users face ongoing threats from Spyware and similar techniques. EPIC supported the Counter Spy Actbut cautioned that a federal spyware law should not replace stronger state laws. EPIC also urged the Senate to address new surveillance techniques, such as deep packet inspectionand Social Networkingadvertising. (June 11, 2008)
- FTC Asked to Stop Stalker Spyware. EPIC's Domestic Violence and Privacy Projectfiled a complaint with the Federal Trade Commissionagainst several purveyors of stalker spyware. Stalker spyware products are over the counter surveillance technologies sold for individuals to spy on other individuals. The complaintalleges that these companies engage in unfair and deceptive practices by: (1) promoting illegal surveillance; (2) promoting "Trojan Horse" email attacks; and (3) failing to warn their customers of legal dangers of misuse of stalker spyware. The FTC is asked to investigate these companies, stop these practices, and seek compensation for victims. (March 6, 2008)
- GPS, Spyware Used by Abuser to Stalk. A woman's ex-husband planted a GPS cell phone in her car, allowing him to find her location and listen to her communications. He further used spyware to obtain her personal information from her computer. The technology enabled him to extend his abuse beyond his physical presence, and to thus extend his power and control. He was sentenced to 8 months in jail. (Oct 1, 2006)
- Spyware Purveyor and Users Indicted. The creator and several users of the "Loverspy" program were indicted on federal cybercrime charges. For a fee, users would craft a greeting card to send to a surveillance target. The card actually installed the "Loverspy" program, which monitored the emails, passwords, and web browsing of the target computer. 1000 purchasers had sent spyware to 2000 victims before the service was shut down by the FBI in 2003. (Aug. 26, 2005).
Introduction
Surveillance technologies and services are available at the consumer and individual level. Technologies used by the government or employers for legal surveillance can be used by those entities as well as individuals for illegitimate activities. Technologies are available to track location. Spies can intercept all manner of communication such as audio, email, instant messaging, text messaging, and computer passwords. Video cameras can surveil a person's activity in the home or bedroom. Providers of these technologies often tout their surreptitious abilities and promote the interpersonal surveillance features. The improper use of these technologies is a clear harm to privacy.
Some abusive relationships have skewed power and control dynamics. These technologies can further skew these dynamics -- the abuser is able to control their victim's life to an even greater extent. The technologies also allow new abuses to be perpetrated: spyware can collect personal information to be used for identity theft; location tracking allows much more enhanced stalking, or even just the knowledge gained from the surveillance can be used to intimidate the victim. Knowing that one is or may be under surveillance can have a disempowering and paralyzing effect.
Individual uses of these technologies may be harder to detect because they exploit a trust between individuals. Despite trust, individual use may be harder to avoid because victims may be coerced into accepting the surveillance. Even once the illegitimate use is detected and the victim wants to complain, the law may not offer much practical help. Illegitimate uses have lead to criminal and civil lawsuits, but there may remain many uses which are essentially unaccountable.
Technologies
Global Positioning System (GPS) devices function by contacting satellites and determining a user's location. GPS devices are available in handheld form. Hikers, boaters, and drivers use GPS for orienteering and navigation. But if the location information is made available to others, then the device can be used for surveillance. Some have the capability to perform "geofencing" where certain boundaries are defined and an alert is generated when someone leaves or enters a given area.
For surveillance purposes, there are two types of GPS devices: active and passive. Active devices continuously communicate their present location to a third party. Thus they allow "real-time" or near instant tracking of the GPS device from another location. This information is not sent from the device to the third party via the GPS satellite system. The device must have another means of communicating its present location to the third party service.
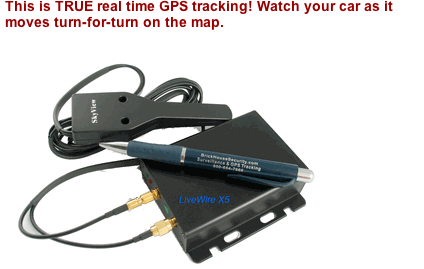
An example of an active GPS tracking device
Passive devices store the location tracking information of its movement on the device. At regular intervals, one has to download the information from the passive GPS device. Only once it is downloaded can a third party see where the GPS device went.

A passive GPS tracking device, notice the USB connector, which is used to download the location data periodically.
Most mobile phones can be set to be active location tracking devices. The FCC's E911 rules require mobile phones to provide location information to 911 dispatch centers. The current rules require a carrier to have up to 67% of their calls to provide location to 50 meters, and 95% to 150 meters accuracy. Carriers may use network based triangulation tools or handset based location tools, such as GPS. This legal requirement has spurred an industry of "location based services" tied to mobile phone devices. One carrier offers a "family locator" service that permits real time tracking of other family members over a website or another handset. Another offering is a social location tracking, allowing one to share one's location with friends, find friends nearby, or tag one's photos with the location.
These services have the potential to be used for surveillance when the user does not know about its presence or has been coerced into accepting it.
Computer & Communications Surveillance
Electronic communications are subject to personal surveillance at various stages. "Keyloggers" record the keystrokes typed on a computer. These can be in a piece of hardware installed in the keyboard wires or can be software in the computer. These allow one to capture anything typed, including passwords. A hardware key logger will not be detected by anti-virus or anti-spyware technologies because it is not a program running on the computer.
A keylogger device, plugged in between the keyboard and computer.
"Screenshot" software regularly takes images or video of what is happening on the screen. These allow one to read messages as they are composed or read by the subject, see what files are edited, and what websites are visited.
"Spyware" can include both of those features plus the ability to intercept, save, and re-route email and other communications sent to or from that computer. Spyware can also access other files on the computer. It can activate a computer's microphone or camera, allowing the spy to listen to what is happening around the computer or see through its camera. Some spyware saves the information captured on the computer itself, requiring one to later access the computer to retrieve it. Others allow remote surveillance. The remote surveillance can send the data to the spy's computer, to a server that the spy connects to at will, or via emails to the spy. Some spyware can be removed by anti-spyware and anti-virus software.

Advertisement for the "Remote Spy" spyware.
"Trojans" are programs that appear to be legitimate and wanted, but then perform a hidden malicious function. The name refers to the Homeric "Trojan Horse," which masquerades as a gift but is actually an attack. Users are tricked into installing the Trojan by its promise of some desirable feature, such as a greeting card or even anti-virus technology.
"Sniffers" can be placed on a computer or network (wired or wireless) and can listen to all the traffic on the network. This will capture all the traffic on the network, including website visits, emails, and instant messaging communications. Since a sniffer is a passive listening device located on a network, it is hard or impossible to detect.
Even without these technologies, information on a computer can be accessed by others with access to the computer. An email program may download the messages locally, and leave them on the hard drive for other users to find. Your browser can be configured to save its history -- and even some of your passwords -- in several places on your computer. Websites you browse to may leave cookies or items stored on your computer. This leaves behind a digital trace which allows a person to check which sites one has visited.
Audio communications can also be accessed. A home telephone can be bugged with an extension, or the classic case of simply accessing the wires. Telephones may also be used to listen to ambient sounds: some mobile phones can be used as surreptitious listening devices by configuring their settings. A stalker in Washington hid a mobile phone in his victim's dashboard, hooked up to the car battery. He was able to call into the phone to hear conversations of the vehicle occupants. He was also able to use the GPS in the phone to locate the vehicle. Hi-Tech Stalking Devices Extend Abusers' Reach
Software is available which allows one to capture text messages sent via smart phones. Telephone records can also be accessed with the practice of "pretexting." Though this will not reveal the content of communications, it will reveal who one is talking with. See EPIC's page on CPNI(Costumer Proprietary Network Information -- the information phone companies collect about costumer's telephone calls).
Video Surveillance
Home video surveillance can be accomplished with hidden "spycams." These cameras can be easily concealed because of their size. Others are sold concealed in items like a bedside alarm clock, a smoke alarm, or wall clock. Some connect to a computer and can upload their images immediately to a website. Some are also available in wireless format, making installation easier and detection harder because wires are not needed. Such a system may also be more susceptible to unauthorized use.
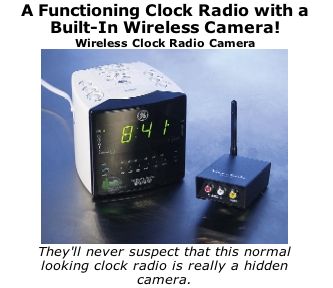
Wireless bedside clock/camera, advertised for surreptitious use.
Legal Issues
The Wiretap Act and Electronic Communications privacy act prohibit the interception of wire, oral and electronic communications. Oral communications protected are limited to those where a person reasonably expects that the communication will not be overheard. "Wire" communications are oral communications that travel over a wire or cable in whole or in pat. "Electronic" communications includes computer signals but does not include wire or oral communications. Besides interception, the law also prohibits disclosing and using the contents of a communication when one knows these are the result of an improper interception. Violations of these provisions lead to criminal and civil penalties.
The federal law in this area is what is called a "one party consent" rule. This means that any one party to the conversation may record it, disclose or use the contents of the conversation. However, some states require all parties to consent. This means that if one is attempting to record a conversation with another, one must give notice to that other person that recording is going on. This has significant implications for those that want to use recording devices to gather evidence and defend themselves.
One complication that arises in the area of computer surveillance is that screenshot software may not count as an "interception" of a communication -- because the screen capture is being made after the message has been delivered. However, other laws may apply. Further, the spy may be misusing the captured information to break other laws.
The Stored Communications Act forbids accessing communications "in electronic storage." The definition of electronic storage does not include, however, emails that have been downloaded to a person's computer. The electronic storage that the law is talking about is only that which is "temporary, intermediate" storage that is "incidental to transmission" or backups kept by the provider. This would apply to people who improperly download your email before you get the chance to.
The Computer Fraud and Abuse Act prohibits intentional unauthorized access to a computer that obtains information from that computer, when the conduct involves interstate or foreign commerce. Accessing information for fraud, or causing damage to computers, if certain minimums are reached is also prohibited. Also of relevance is its prohibition on trafficking in passwords with the intent to defraud. Spyware technologies, keyloggers and screenshot software can meet this definition. But there will still have to be shown that there was an intent to spy and a lack of authorization.
Users of "Eblaster" have been prosecuted for using it for spousal surveillance. " Man Accused of Installing Spy Software to Monitor Estranged Wife's Computer Use." Court TV News, Sept. 6, 2001. Eblaster is a commercially available software that records emails, instant messages, passwords, and websites visited. The reports are emailed to the spy.
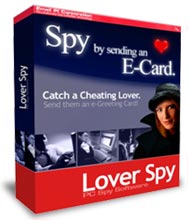
Advertisement for the Loverspy program.
The maker and some users of "Loverspy" software were indicted for the manufacture, sale and use of computer spyware. DOJ Press Release. The Loverspy indictment describes how the software operated:
Specifically, Loverspy was touted to surreptitiously monitor, record and report all electronic mails, passwords, chat sessions, instant messages and websites visited by any user of the victim computer. Loverspy claimed to provide the spy with remote access to all files on the victim computer(s) including the ability to modify and delete files, and provided the spy with the ability to see exactly what the victim user was seeing on the victim's computer monitor . . . . Lover spy was designed, according to its marketing materials, with stealth in mind, claiming that it would be impossible to detect by 99.9% of users. Loverspy was designed so that it could be remotely installed, arriving hidden in an innocuous-appearing electronic greeting card sent by electronic mail . . . . When a victim opened the card, Loverspy surreptitiously would install itself on the victim computer and immediately being to collect information. Anti-virus software in use during the period of time relevant to this indictment did not identify Loverspy as dangerous and, as a consequence, did not block the installation of the software.
The maker of the software was charged under several provisions of the Wiretap Act and the Computer Fraud and Abuse Act: Manufacturing a Surreptitious Interception Device (18 U.S.C. Sec. 2512(1)(b); Sending a surreptitious Interception Device. 18 U.S.C. Sec. 2512(1)(a); Advertising a surreptitious Interception Device. 18 U.S.C. Sec. 2512(a)(c)(i); Unlawfully Intercepting Electronic Communications. 18 U.S.C. Sec. 2511(1)(a); Disclosing Unlawfully Intercepted Electronic Communications. 18 U.S.C. Sec 2511(1)(c); and Unauthorized Access to Computer for Financial Gain. 18 U.S.C. Secs. 1030(a)(2)(C) and 1030(c)(2)(B)(i).
Some jurisdictions provide for spousal immunities in inter-spousal espionage. Most locations do not. The Fifth circuit in Simpson v. Simpson, 490 F.2d 806 (1974) applied the immunity in the case of a husband surveilling his wife, whom he suspected of cheating. Most other federal courts do not have this immunity. Simpson v. Simpson was overturned in parts of the old 5th Circuit that are now the 11th Circuit in Glazner v. Glazner. 347 F. 3d 1212 (2003). The Second circuit has also immunized spouses from federal wiretap law. Anonymous v. Anonymous, 585 F.2d 677 (1977).
Another complication are the user practices of individuals who have a shared family computer. Sharing a computer without individual passwords may be interpreted as authorizing the other individual to read the contents of emails or files on the computer. Likewise if the computer is considered marital property, both parties may have equal access to the information on it.
Video Surveillance
Wiretap law does not prohibit the capturing of visual images, only oral or electronic communications. The Video Voyeurism Prevention Act prohibits the capturing of images of a person's "private areas" under circumstances in which they would have a reasonable expectation of privacy. A "private area" is basically the area that is covered by undergarments, whether worn or not.
Privacy Torts and Stalking
Some states have recognized all or some of the privacy torts. These are intrusion upon seclusion; public disclosure of private facts; publicity which places a person in a false light; and appropriation of name and likeness. Personal surveillance which rises to a substantial interference with the seclusion of another in a highly offensive way may be actionable as a privacy invasion. There may be practical problems with actually proving this, as some courts might not recognize seclusion or privacy within a marriage or other family relation. The tort of intentional infliction of emotional distress may also be available to individuals. This would cover only "extreme and outrageous" conduct which was intended to cause sever emotional distress.
Some surveillance can rise to the level of stalking. The National Center for Victims of Crime's model stalking codedefines stalking as:
Any Person who purposefully engages in a course of conduct directed at a specific person and knows or should know that the course of conduct would cause a reasonable person to:
(a) fear for his own safety or the safety of a third person; or
(b) suffer other emotional distress,
is guilty of stalking
Surveillance can cause a fear for safety when location or other information is gathered. Surveillance can cause emotional distress. The distress can last beyond the immediate surveillance -- as someone who has been victimized by one or more forms of surveillance may shut down from other activities. Users of GPS devices have been convicted of stalking. " Californian Gets 16 Months for Stalking by Satellite," USA Today, Jan 29. 2005.
News Articles Related to Personal Surveillance
- FTC get CyberSpy's RemoteSpy banned in the U.S., Geek.com, Nov. 20, 2008.
- Commercial Spyware Vendor Hit with Restraining Order, Softpedia, Nov. 20, 2008.
- Court Halts Sale of DIY Spyware, Wired, Nov. 19, 2008.
- US court stops sale of commercial spyware, Heise Online, Nov. 19, 2008
- Teens Charged With Loading Spyware, Changing Grades, ABC News, June 19, 2008.
- Feds execute search and seizure at County Councilman Tony Trout's home: Spyware used to get administrator's passwords, witness tells FBI agent, Greenville Online,June 13, 2008.
- Targets of Spying Get Smart, Wall Street Journal,June 11, 2008.
- Nigerian gets 18 months for cyberattack on NASA employee, ComputerWorld, May 1, 2008.
- Suspicious spouses turn to spyware, TheAge, February 1, 2008.
- Tech aplenty for cheaters, suspicious spouses, MSNBC.com, December 12, 2007.
- Arrest of Identity Theft's Bonnie and Clyde Opens Debate on Spyware programs, Digital Journal,December 5, 2007.
- Spying on Lovers Email? Monitoring May Be Illegal, Austin American-Statesman ,November 13, 2007.
- Stalkers Go High Tech to Intimidate Victims, Washington Post, April 14, 2007.
- Hi-Tech Stalking Devices Extend Abuser's Reach, Women's E-News,October 1, 2006.
- Creator and Four Users of Loverspy Spyware Program Indicted, Department of Justice ,August 26, 2005.
- Man Accused of Installing Spy Software to Monitor Estranged Wife's Computer Use, Court TVnews, September 6, 2001.
Other Resources
- EPIC Gender and Privacy Page.
- EPIC Video Surveillance Page.
- Stalking Resource Center.
- Anti Spyware Coalition.
- Department of Justice Cybercrime Section.
- Federal Trade Commission Spyware Alert.
- State Spyware Legislation.
Share this page:
Subscribe to the EPIC Alert
The EPIC Alert is a biweekly newsletter highlighting emerging privacy issues.







